Bechtle Clouds Portal
Multi Factor Authentication
MFA - Documentation
In the modern world where the use of the Internet and other networks is mainstream, security becomes a critical issue. These days, it is possible to extend the traditional login/password authentication method to provide additional layers of security. The multi-factor authentication (MFA) method requires the user to provide two or more verification factors to access a required resource (an application or VPN). MFA protects user accounts from unauthorised access. This document is intended for the end users who are authorised to access the Bechtle Clouds Portal. The document provides step-by-step instructions for specific use cases.
Case 1 - Classic authentication
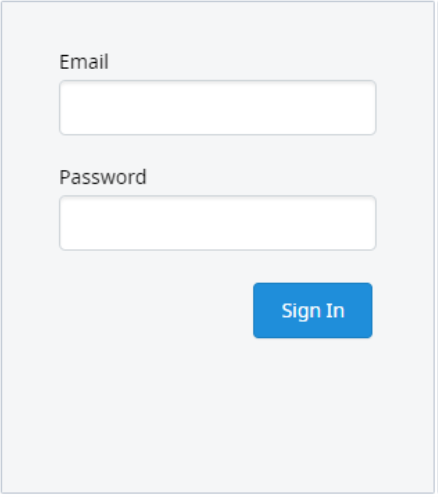
You can obtain access to the Bechtle Clouds Portal from your personal contact within the Bechtle Group. For this purpose, an automatic mail with initial login data is generated. This mail address is also used as a communication channel for notifications and error messages. When logging in, you will be asked to enter a personal security password.
Figure 1 Classic login
Case 2 - Multi-factor authentication
The idea of MFA is to get additional verification information (factors) from the user. In the Bechtle Clouds Portal, this factor is a one-time code (OTC) - a code that you generate via a mobile application. The mobile application should be installed on your mobile phone or other device. The secure connection is guaranteed if the OTC is directly in your hand on your personal mobile phone when you log into the Bechtle Clouds Portal.
Initial login
When you open the Bechtle Clouds Portal for the first time after the changeover, the login page is displayed. Enter your user name and password and confirm with Log in. The application will guide you to an initial 3-step configuration for your mobile device.
Figure 2 Initial configuration
Step 1:
Install one of the suggested applications on your mobile device: FreeOTP, Google Authenticator or Microsoft Authenticator (this list may vary depending on the administrator's settings). You can find them in the Google Play Market, App Store or on the Microsoft website. All of these applications are equally suitable for you. Follow the instructions when you install them.
Step 2:
Open the app installed on your device for the first time. Scan the QR code with your mobile phone. This will activate the mobile application to generate the OTC. By default, an OTC remains valid for 30 seconds before the next code is generated.
Tip:
To perform a QR code scan, you should have this feature installed on your mobile phone. Otherwise, you can click on the "Unable to scan?" link. Some mobile apps may request additional configuration details to set up the OTC generation algorithm.
Step 3:
Enter the specified OTC and click "Submit". You can optionally enter the device name. Enter 'phone' for this. If you omit this, the device will be identified as 'unnamed'.
Figure 3 Initial login
Future logins
The next time you log in to the Bechtle Clouds Portal, proceed as follows.
Step 4:
On the login page, enter your login and password as described in the Classic Authentication section. The pop-up for entering your one-time code is displayed.
Figure 4 - OTC Login
Step 5:
Open your mobile application as described in step 2. Read (or copy) the OTC displayed there. Click on Log In.
Figure 5 - OTC entry
Lost device
If your device is lost or stolen, you should contact our support team at cloud.support@bechtle.com to have the MFA settings assigned to the lost device reset. This will invalidate the one-time codes generated on your stolen device so that your device can no longer be used to generate OTCs.